Raymii.org

אֶשָּׂא עֵינַי אֶל־הֶהָרִים מֵאַיִן יָבֹא עֶזְרִֽי׃Home | About | All pages | Cluster Status | RSS Feed
My Yubikey broke, but I had a backup. So should you with your 2FA
Published: 18-03-2018 | Author: Remy van Elst | Text only version of this article
❗ This post is over eight years old. It may no longer be up to date. Opinions may have changed.
Table of Contents
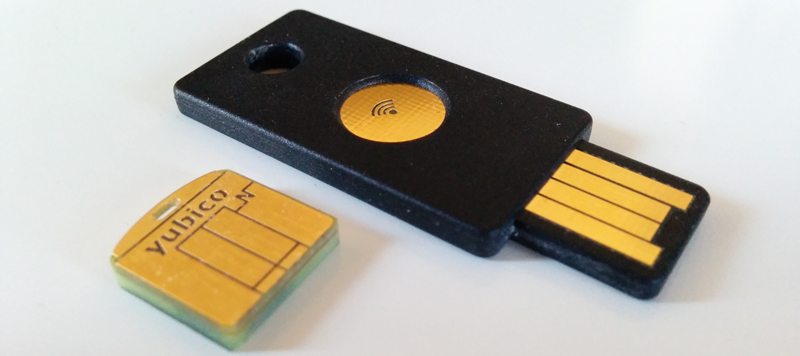
Today my trusty old first generation Yubikey didn't light up when I plugged it in. No problem for me, I had a backup key. But most people don't, so here's an important tip when you use two factor authentication like a Yubikey, Nitrokey or Google Authenticator (HOTP). TL;DR: Have a second hardware token stored away safely and backup your QR codes (print/screenshot) somewhere secure. Swap the hardware tokens often to make sure they both work with all services. Today my trusty old first generation Yubikey didn't light up when I plugged it in. No problem for me, I had a backup key. But most people don't, so here's an important tip when you use two factor authentication like a Yubikey, Nitrokey or Google Authenticator (HOTP). TL;DR: Have a second hardware token stored away safely and backup your QR codes (print/screenshot) somewhere secure. Swap the hardware tokens often to make sure they both work with all services.
As we all know, 2 factor authentication is important. Passwords are insecure, can be brute forced or logged (malware, keylogger) and are re-used everywhere. If you're password is leaked, when you are using two factor, something you know (password/username) and something you have (security token, time-based code), the attacker doesn't have access to your stuff unless they also compromise the second factor.
I love security devices, I've written a lot about the open source NitroKey devices, even how to get the private key fronm the HSM. Also, the FST-01, an open source GnuPG token and the SmartCard-HSM. In my professional job I work with enterprise HSM devices (Safenet, Gemalto).
Backups backups backups!
This tip applies both to HOTP tokens (Google Authenticator) and hardware tokens.
HOTP / TOTP
If you use Google Authenticator (or any other TOTP/HOTP), you get a QR code to scan with your device or a code to enter. Screenshot that code and print it, file it in a folder. Or write down the code.

I myself have a second Android device at home with all the codes scanned as well, so when my main phone breaks I have an 'online' backup. Since the codes are all printed, when my main phone is working again, I scan the codes from the 'offline' backup to add them back. I don't have to login to every service or contact customer support to change the 2 factor settings.
Hardware tokens

The physical tokens, like the Yubikey, GnuPG (FST-01 or Nitrokey Start/Pro), SmartCard HSM, Nitrokey HSM or the RSA token, yes my keychain is full with those sadly, all have a second device. At home I have a 'backup' keychain with authentication tokens. Which means, a second Yubikey (for KeePass), a second Nitrokey Pro (for GPG) and a second Nitrokey HSM (S/MIME and other certificates). It also has copies of the important physical keys (car, home, etc).
This keychain is stored in a safe next to the phone with the authenticator and the printed QR codes. Also a printout of my private keys which are not in hardware tokens (with passwords).
You must also add all these devices to the services you use. Lastpass for example supports up to 5 yubikeys. It's not much use to have a second YubiKey if you can't use it. So make sure to add the token to the service you use.
In the case of the GPG token and the HSM, backup the key material on them and import it on the second device.
The last step in this backup scheme is, as is with all backups, to regularly test them. Otherwise a backup is worth nothing. I swap the keychain once every month, so I know it works with all the services it needs to. If something doesn't work, I don't want to find out on a critical moment, rather as soon as possible. Just as with all other backups, do a restore test once in a while.
I know that this increases the cost, instead of 1 token you need to buy two, and Yubikeys are pricey ($50 as of today). But I had my two Yubikeys since around 2010, so 8 years, that is a cost I could spread out. The other hardware tokens are either bought via my work (free for me yay) or paid for myself. But, my time is costly, so I rather buy two tokens than to spend an afternoon fixing all the 2 factor authentication.
Tags: backups , blog , hotp , lastpass , nitrokey , password , security , yubikey