Raymii.org

אֶשָּׂא עֵינַי אֶל־הֶהָרִים מֵאַיִן יָבֹא עֶזְרִֽי׃Home | About | All pages | Cluster Status | RSS Feed
Let's Encrypt with DirectAdmin, now built in!
Published: 24-02-2016 | Author: Remy van Elst | Text only version of this article
❗ This post is over ten years old. It may no longer be up to date. Opinions may have changed.
Table of Contents
Let's Encrypt is a new certificate authority, recognized by all major browsers. They make it a breeze to set up TLS certificates for your web server. And for free! Let's Encrypt is supported by major players like Mozilla, Akamai, Cisco, the EFF, the Internet Security Research Group and others. Let's Encrypt provides free, automatic and secure certificates so that every website can be secured with an SSL certificate.
I have written a guide on using Lets Encrypt with Directadmin before, but that involved manually logging in via SSH and a lot of work.
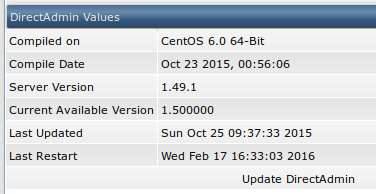
DirectAdmin now supports Lets Encrypt natively since version 1.50, so no more ssh fiddling, just via the control panel, for all the users on the server.
The previous article still applies and it still works. It's generic enough for all control panels and non-supported webservers by Let's Encrypt.
So let's get started. We'll do a couple of things, namely:
- Update Directadmin
- Enable Let's Encrypt
- Request a certificate
- ???
- Profit!?!??!
After step 3, everything is automatic, including renewals.
Do note that the last step of the article requires you to have set up a website and a domain already. They must be working and resolving in DNS, because Let's Encrypt triggers a challenge-response authentication to the domain name.
You can test with a subdomain as well, but make sure to add the subdomain as a new domain, not as a subdomain (So, Domain Administration, Add a domain, testsub.example.org). Actual subdomains don't support seperate SSL in Directadmin.
Do note that I'm not sponsored by Directadmin (Hi John and crew) nor by Let's Encrypt. I just like them a lot both, Directadmin for being a lightweight but very easy and functional controlpanel, and Let's Encrypt for their effort to secure the entire web for free.
Update Directadmin
Remember when I said no more fiddling with SSH? Well, that part isn't entirely untrue. You need to login once via SSH to update Directadmin and enable Let's Encrypt.
You can update Directadmin via the Administrator Settings -> Update / Licensing page as well, but I like the custombuild method better. Why? Because you can update the other parts of your server as well and that a general good thing to do.
Also, you do need to login via SSH and execute a few other steps like enabling Let's Encrypt and rewriting the configuration files, so you might just as well login and update via Custombuild.
A friend of mine wrote a great article on keeping Directadmin up to date on her website. I'll give you the TL;DR version here, but, if you want to know more, read her article.
First log in to your server via SSH as root or as a user that can sudo to
root. Navigate to the custombuild folder:
cd /usr/local/directadmin/custombuild/
Clean up earlier updates to make sure no weird quirks show up:
./build clean all
Update the software list:
./build update
If you want, you can get a list of the updates available:
./build versions | grep is
Output is like this:
DirectAdmin 1.49.1 to 1.50.0 update is available.
cURL 7.46.0 to 7.47.1 update is available.
FreeType 2.6.2 to 2.6.3 update is available.
MySQL 5.6.28 to 5.6.29 update is available.
PHP 5.6 (mod_php) 5.6.17 to 5.6.18 update is available.
Apply the updates:
./build update_versions
If you only want to update Directadmin and not the other updates you can do that with the following command:
./build update_da
While you're applying updates, do the operating system updates as well:
apt-get update && apt-get upgrade || yum update
The above command will work on both Debian / Ubuntu and CentOS. You will be asked to confirm the updates before they're installed.
There is one more important thing to do and that is rewriting the configuration. You need to do this because Directadmin keeps all the challenge-response files in one place, not for all domains seperate. Directadmin's Custombuild has a function for this. Do note that if you did any manual changed (not via Directadmin), they will be lost. Make sure you have a backp. Rewrite the confs, still in the custombuild folder:
./build rewrite_confs
Now that your server is up to date, continue on to enable Let's Encrypt in Directadmin.
Enable Let's Encrypt
Make sure you're still logged in via SSH. You can execute the below command and it will add the configuration to the Directadmin configuration, but only if it's not already there:
grep -q 'letsencrypt=1' /usr/local/directadmin/conf/directadmin.conf || echo 'letsencrypt=1' >> /usr/local/directadmin/conf/directadmin.conf
You can also manually edit the file
/usr/local/directadmin/conf/directadmin.conf and add the following value:
'letsencrypt=1'
If your server is recent enough, CentOS 6, Ubuntu 12.04 and you run Apache 2.2
or higher, you can also enable SNI support (Server name indication). That
is an extension to the TLS protocol which, simply said, allows you to host
multiple SSL enabled sites on one IP address.
Almost the same command as above, but with another value:
grep -q 'enable_ssl_sni=1' /usr/local/directadmin/conf/directadmin.conf || echo 'enable_ssl_sni=1' >> /usr/local/directadmin/conf/directadmin.conf
After changing the configuration, restart Directadmin:
service directadmin restart
You can check via the web interface if you now have the most recent version:
Request a certificate
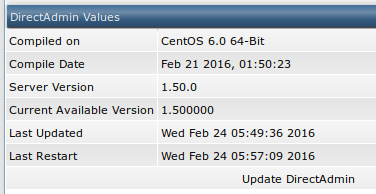
Now that we're all set up we can request a certificate for a website. Do make sure the user and the package have SSL enabled in their settings, otherwise add that option to the account.
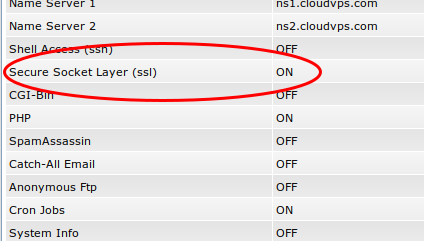
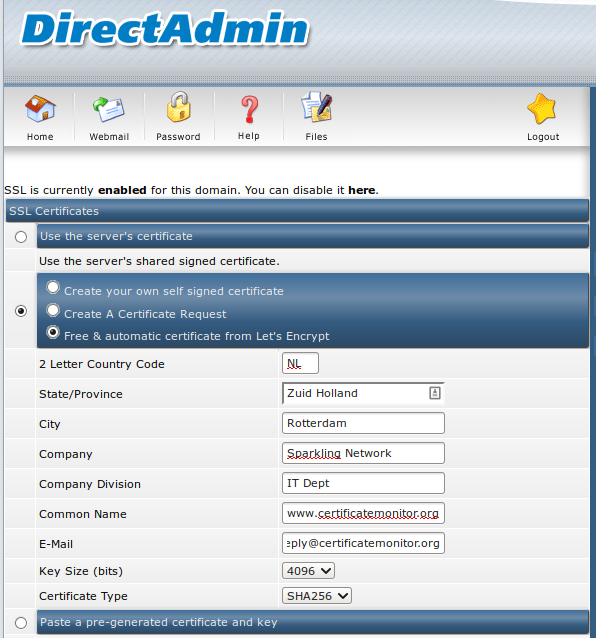
Log in as the user you want to request the certificate for (either with their username and password or via the "Admin" -> "Show all users", "username", "Login as username"). Navigate to "Advanced Features" -> "SSL Certificates".
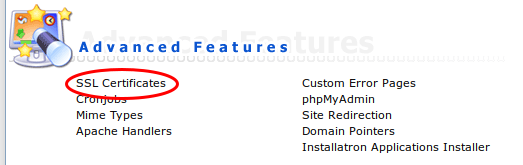
Make sure the top line says: SSL is currently enabled for this domain. You can
disable it here.
If it says SSL is currently disabled for this domain. You can enable it here.,
click the Enable it here link and turn it on, then go back to the "SSL
Certificates" page.
Select the third option, Free & automatic certificate from Let's Encrypt and
fill in the fields below.
If you've set up everything correctly, that meaning updated Directadmin, rewrote the configuration and enabled Let's Encrypt you should have output like in the picture below, with a correctly and valid certificate.
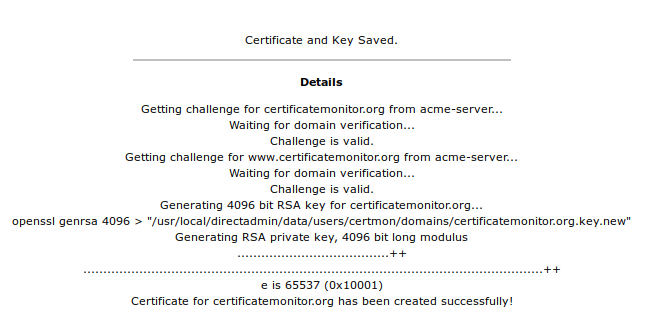
You can check if it all worked by using my SSL Check over at SSLdecoder.org.
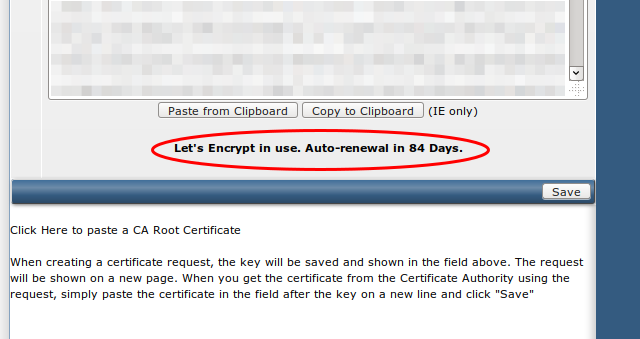
Directadmin will also show you that Let's Encrypt is enabled, plus the auto- renew date.
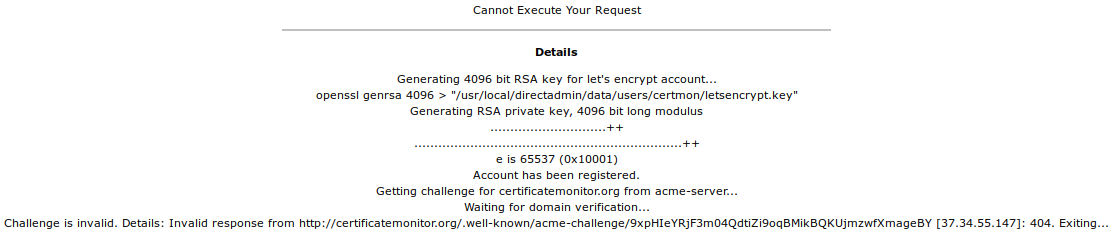
If you forgot to rewrite the configuration, you might get an error message like in the picture below. Go back and re-do everything in this tutorial, don't forget to rewrite the configuration and try again.
That's all there is. Your website is now set up with a certificate for free, which will auto renew when it's about to expire. You don't have to do anything or worry about it anymore.
Profit!?!?!?!
Another subtopic? But we're already done, the site has a certificate and it all works? I know, I know. There are a few things you might want to do to make sure it all keeps working in the best state.
First, to make sure the certificate doesn't expire, add your website to the free Certificate Expiry Monitor service, one of my other projects. The renew process should be automatic, but you never know. Even Google sometimes forgets to renew certificates, so better to make sure it won't happen to your sites.
Second, you can optimize all aspects of TLS and make sure it's very secure. I have a guide on that for Apache, the Mozilla Foundation has one as well. Both are very good, explain all aspects and make sure your site is as secure as possible.
Third, check your score, settings and ratings on an SSL/TLS tester like SSL Labs or my own, faster check, the SSL Decoder, which is open source as well.
Tags: apache , articles , centos , certificate , directadmin , nginx , openssl , ssl , tls