Raymii.org

אֶשָּׂא עֵינַי אֶל־הֶהָרִים מֵאַיִן יָבֹא עֶזְרִֽי׃Home | About | All pages | Cluster Status | RSS Feed
OSSEC 2.8 Server, Client, Web UI and Analogi Dashboard Installation tutorial
Published: 11-06-2014 | Author: Remy van Elst | Text only version of this article
❗ This post is over eleven years old. It may no longer be up to date. Opinions may have changed.
Table of Contents
OSSEC is an Open Source Host-based Intrusion Detection System that performs log analysis, file integrity checking, policy monitoring, rootkit detection, real- time alerting and active response. It runs on most operating systems, including Linux, MacOS, Solaris, HP-UX, AIX and Windows. It also includes agentless monitoring for use with for example Cisco, HP or Juniper hardware.
OSSEC 2.8 was released on the 4th of June, 2014. You can find the full release notes here. New features include outputing of all alerts to a zeromq PUB socket in JSON, more sshd rules and a lot of bugfixes.
This tutorial covers the installation of the OSSEC 2.8.0 server, the standard OSSEC Web UI and the Analogi dashboard on Ubuntu 14.04. It also covers OSSEC setup with MySQL support. Last but not least it shows you how to install the OSSEC agent on a *NIX system.
This tutorial is written for an Ubuntu 14.04 OSSEC 2.8.0 server, but can be easily adapted to other *NIX operating systems. It only covers basic OSSEC client/server configuration. It gets you started, the rest is available in the documentation: http://www.ossec.net/doc/
You can read the tutorial for OSSEC 2.7 on Ubuntu 12.04 here.
Requirements
- An Ubuntu 14.04 server
- Apache2, PHP, MySQL and development packages
- OSSEC clients to monitor (*NIX or Windows machines, Cisco switches etc).
Installing development packages
OSSEC is installed from source, therefore you need development packages. This is both for the OSSEC clients as for the OSSEC server:
apt-get install build-essential make libssl-dev git
Installing Apache, MySQL and PHP
This is fairly simple on Ubuntu. It is all covered with apt:
apt-get install mysql-server libmysqlclient-dev mysql-client apache2 php5 libapache2-mod-php5 php5-mysql php5-curl php5-gd php5-intl php-pear php5-imagick php5-imap php5-mcrypt php5-memcache php5-ming php5-ps php5-pspell php5-recode php5-snmp php5-sqlite php5-tidy php5-xmlrpc php5-xsl
Remember to set a strong root password for MySQL. Next finish MySQL with a secure installation:
mysql_secure_installation
Accept all the suggested options. Now restart all requires services:
/etc/init.d/apache2 restart
/etc/init.d/mysql restart
Compiling the OSSEC server
Do note that OSSEC has Debian packages available. These do not include MySQL or Postgres support, therefore we need to compile it. The packages are also at the moment only available for OSSEC 2.7.
Download and verify OSSEC, either via wget or from the website: http://www.ossec.net/?page_id=19
wget http://www.ossec.net/files/ossec-hids-2.8.tar.gz
md5sum ossec-hids-2.8.tar.gz
ossec-hids-2.8.tar.gz: 90f3c54f22abe9c07661fb51ddaa8474
From the OSSEC website:
MD5(ossec-hids-2.8.tar.gz)= 90f3c54f22abe9c07661fb51ddaa8474
SHA1(ossec-hids-2.8.tar.gz)= 1d72a8cd347379ef7a533ba9633231c5bfedfa1a
If it is correct, then extract it:
tar -xf ossec-hids-2.8.tar.gz
cd ossec-hids-2.8
Database support
The Makefile error is fixed in 2.8.
This tutorial uses MySQL because the Analogi dashboard only supports MySQL. Instructions for Postgres are included.
Enable database support:
cd src
make setdb
Error: PostgreSQL client libraries not installed.
Info: Compiled with MySQL support.
If you want postgres support, install postgresql-server-dev-9.3.
Continue with the compilation/installation:
cd ../
./install.sh
** Para instalao em portugus, escolha [br].
** , [cn].
** Fur eine deutsche Installation wohlen Sie [de].
** , [el].
** For installation in English, choose [en].
** Para instalar en Espaol , eliga [es].
** Pour une installation en franais, choisissez [fr]
** A Magyar nyelv teleptshez vlassza [hu].
** Per l'installazione in Italiano, scegli [it].
** [jp].
** Voor installatie in het Nederlands, kies [nl].
** Aby instalowa w jzyku Polskim, wybierz [pl].
** , [ru].
** Za instalaciju na srpskom, izaberi [sr].
** Trke kurulum iin sein [tr].
(en/br/cn/de/el/es/fr/hu/it/jp/nl/pl/ru/sr/tr) [en]:
OSSEC HIDS v2.8 Installation Script - http://www.ossec.net
You are about to start the installation process of the OSSEC HIDS.
You must have a C compiler pre-installed in your system.
If you have any questions or comments, please send an e-mail
to dcid@ossec.net (or daniel.cid@gmail.com).
- System: Linux ossec 3.13.0-24-generic
- User: root
- Host: ossec
-- Press ENTER to continue or Ctrl-C to abort. --
1- What kind of installation do you want (server, agent, local, hybrid or help)? server
- Server installation chosen.
2- Setting up the installation environment.
- Choose where to install the OSSEC HIDS [/var/ossec]:
- Installation will be made at /var/ossec .
3- Configuring the OSSEC HIDS.
3.1- Do you want e-mail notification? (y/n) [y]:
- What's your e-mail address? user@example.org
- What's your SMTP server ip/host? smtp.gmail.com
3.2- Do you want to run the integrity check daemon? (y/n) [y]:
- Running syscheck (integrity check daemon).
3.3- Do you want to run the rootkit detection engine? (y/n) [y]:
- Running rootcheck (rootkit detection).
3.4- Active response allows you to execute a specific
command based on the events received. For example,
you can block an IP address or disable access for
a specific user.
More information at:
http://www.ossec.net/en/manual.html#active-response
- Do you want to enable active response? (y/n) [y]:
- Active response enabled.
- By default, we can enable the host-deny and the
firewall-drop responses. The first one will add
a host to the /etc/hosts.deny and the second one
will block the host on iptables (if linux) or on
ipfilter (if Solaris, FreeBSD or NetBSD).
- They can be used to stop SSHD brute force scans,
portscans and some other forms of attacks. You can
also add them to block on snort events, for example.
- Do you want to enable the firewall-drop response? (y/n) [y]:
- firewall-drop enabled (local) for levels >= 6
- Default white list for the active response:
- 194.60.207.52
- 194.60.207.53
- 79.170.92.7
- Do you want to add more IPs to the white list? (y/n)? [n]:
3.5- Do you want to enable remote syslog (port 514 udp)? (y/n) [y]:
- Remote syslog enabled.
3.6- Setting the configuration to analyze the following logs:
-- /var/log/auth.log
-- /var/log/syslog
-- /var/log/dpkg.log
-- /var/log/apache2/error.log (apache log)
-- /var/log/apache2/access.log (apache log)
- If you want to monitor any other file, just change
the ossec.conf and add a new localfile entry.
Any questions about the configuration can be answered
by visiting us online at http://www.ossec.net .
5- Installing the system
- Running the Makefile
INFO: Little endian set.
*** Making zlib (by Jean-loup Gailly and Mark Adler) ***
[...]
*** Making cJSON (by Dave Gamble) ***
[...]
*** Making Lua 5.2 (by team at PUC-Rio in Brazi) ***
[...]
*** Making os_xml ***
[...]
*** Making os_regex ***
[...]
*** Making os_net ***
[...]
*** Making os_crypto ***
[...]
*** Making shared ***
[...]
*** Making config ***
[...]
*** Making os_maild ***
[...]
*** Making os_dbd ***
make[1]: Entering directory `/root/ossec-hids-2.8/src/os_dbd'
Compiling DB support with:
cc -g -Wall -I../ -I../headers -DDEFAULTDIR=\"/var/ossec\" -DUSE_OPENSSL -DUSEINOTIFY -DARGV0=\"ossec-dbd\" -DOSSECHIDS *.c ../config/lib_config.a ../shared/lib_shared.a ../os_net/os_net.a ../os_regex/os_regex.a ../os_xml/os_xml.a -o ossec-dbd -I/usr/include/mysql -DBIG_JOINS=1 -fno-strict-aliasing -g -DNDEBUG -L/usr/lib/x86_64-linux-gnu -lmysqlclient -lpthread -lz -lm -ldl -DDBD -DUMYSQL
make[1]: Leaving directory `/root/ossec-hids-2.8/src/os_dbd'
*** Making os_csyslogd ***
[...]
*** Making agentlessd ***
[...]
*** Making os_execd ***
[...]
*** Making analysisd ***
[...]
*** Making logcollector ***
[...]
*** Making remoted ***
[...]
*** Making client-agent ***
[...]
*** Making addagent ***
[...]
*** Making util ***
[...]
*** Making rootcheck ***
[...]
*** Making syscheckd ***
[...]
*** Making monitord ***
[...]
*** Making os_auth ***
[...]
- System is Debian (Ubuntu or derivative).
- Init script modified to start OSSEC HIDS during boot.
- Configuration finished properly.
- To start OSSEC HIDS:
/var/ossec/bin/ossec-control start
- To stop OSSEC HIDS:
/var/ossec/bin/ossec-control stop
- The configuration can be viewed or modified at /var/ossec/etc/ossec.conf
Thanks for using the OSSEC HIDS.
If you have any question, suggestion or if you find any bug,
contact us at contact@ossec.net or using our public maillist at
ossec-list@ossec.net
( http://www.ossec.net/main/support/ ).
More information can be found at http://www.ossec.net
--- Press ENTER to finish (maybe more information below). ---
- In order to connect agent and server, you need to add each agent to the server.
Run the 'manage_agents' to add or remove them:
/var/ossec/bin/manage_agents
More information at:
http://www.ossec.net/en/manual.html#ma
OSSEC is now installed. Restart it:
/var/ossec/bin/ossec-control restart
Configuring MySQL
We need to create a user and database for OSSEC. Open a MySQL shell:
mysql -u root -p
Enter password:
[...]
mysql> create database ossec;
Query OK, 1 row affected (0.00 sec)
grant INSERT,SELECT,UPDATE,CREATE,DELETE,EXECUTE on ossec.* to ossec_u;
Query OK, 0 rows affected (0.00 sec)
set password for ossec_u = PASSWORD('Passw0rd');
Query OK, 1 row affected (0.00 sec)
flush privileges;
Query OK, 0 rows affected (0.00 sec)
quit;
The database also needs a schema. OSSEC provides the schema, it is located in
the extracted OSSEC folder, src/os_dbd.
Import it into MySQL:
mysql -u root -p ossec < src/os_dbd/mysql.schema
OSSEC MySQL configuration
We have to add the database config to /var/ossec/etc/ossec.conf:
<ossec_config>
<database_output>
<hostname>127.0.0.1</hostname>
<username>ossec_u</username>
<password>Passw0rd</password>
<database>ossec</database>
<type>mysql</type>
</database_output>
</ossec_config>
Change type mysql to type postgresql for the PostgreSQL database.
Save it, then enable the database in OSSEC:
/var/ossec/bin/ossec-control enable database
/var/ossec/bin/ossec-control restart
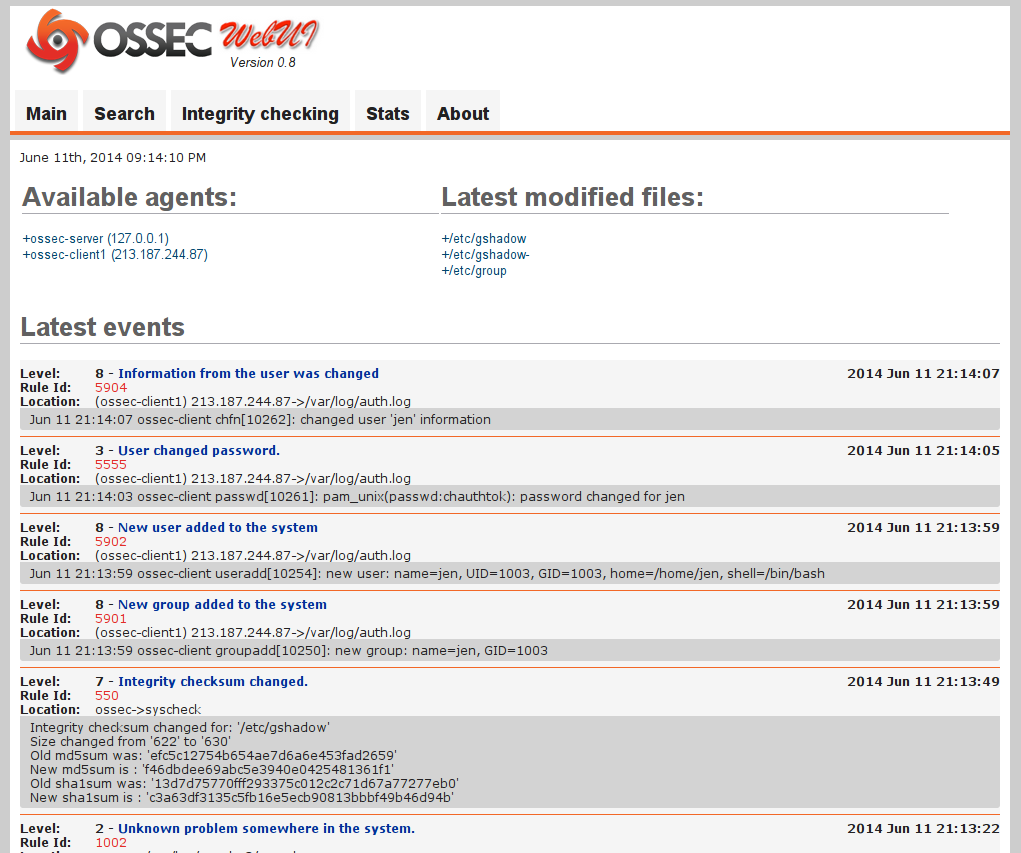
Installing OSSEC Web UI
This is also quite simple. Because we've already set up Apache and PHP, we can
just download the web UI and extract to /var/www/html:
wget http://www.ossec.net/files/ossec-wui-0.8.tar.gz
tar -xf ossec-wui-0.8.tar.gz
mkdir -p /var/www/html/ossec/tmp/
mv ossec-wui-0.8/* /var/www/html/ossec/
chown www-data:www-data /var/www/html/ossec/tmp/
chmod 666 /var/www/html/ossec/tmp
Make sure the www-data user can access the ossec folder:
usermod -a -G ossec www-data
We use version 0.8 of Web UI because there are a lot of errors (like broken
search) in the stable 0.3 version. We also set the correct permissions on the
tmp/ folder. Afterwards the web ui is visible at http://hostname/ossec/.
Installing Analogi Web Dashboard
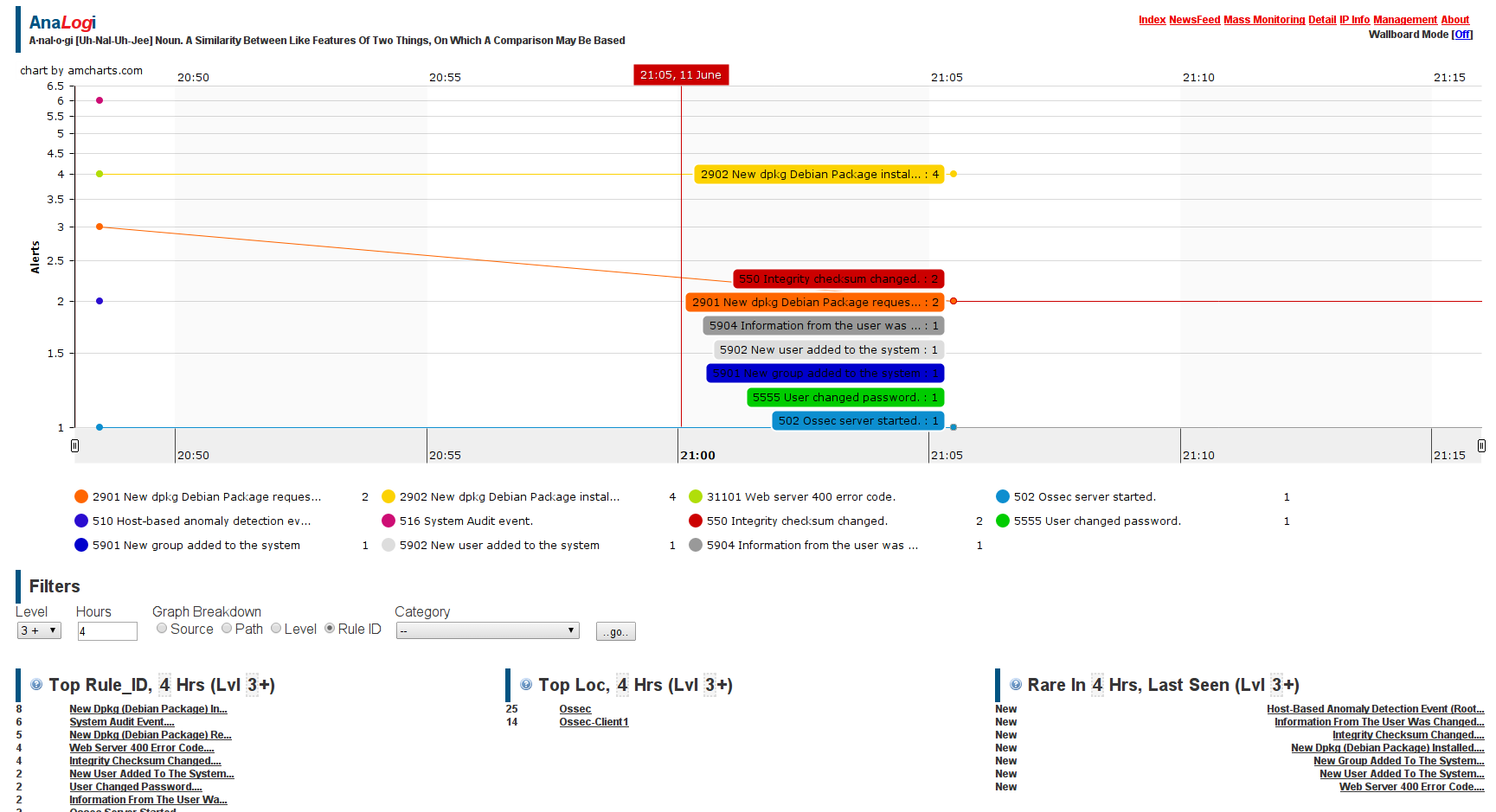
The Analogi dashboard is a nice and informative dashboard around OSSEC, which provides more visual information then the standard Web UI. The standard Web UI has better search functions, the Dashboard can be used for example on a Wall Mounted monitor and such.
Installation consists out of cloning the git repo and editing the settings file:
cd /var/www/html/
git clone https://github.com/ECSC/analogi.git
cp analogi/db_ossec.php.new analogi/db_ossec.php
vim analogi/db_ossec.php
Edit the relevant settings for the MySQL database configuration:
define ('DB_USER_O', 'ossec_u');
define ('DB_PASSWORD_O', 'Passw0rd');
define ('DB_HOST_O', '127.0.0.1');
define ('DB_NAME_O', 'ossec');
When correctly configured the Analogi webinterface can be found at http://hostname/analogi/.
The OSSEC server is now correctly set up.
Client installation
Download and verify the OSSEC 2.8 .tar.gz file as described above. Don't forget to install the development packages. This time, do an agent installation. See the output below:
# ./install.sh
** Para instalao em portugus, escolha [br].
** , [cn].
** Fur eine deutsche Installation wohlen Sie [de].
** , [el].
** For installation in English, choose [en].
** Para instalar en Espaol , eliga [es].
** Pour une installation en franais, choisissez [fr]
** A Magyar nyelv teleptshez vlassza [hu].
** Per l'installazione in Italiano, scegli [it].
** [jp].
** Voor installatie in het Nederlands, kies [nl].
** Aby instalowa w jzyku Polskim, wybierz [pl].
** , [ru].
** Za instalaciju na srpskom, izaberi [sr].
** Trke kurulum iin sein [tr].
(en/br/cn/de/el/es/fr/hu/it/jp/nl/pl/ru/sr/tr) [en]:
OSSEC HIDS v2.8 Installation Script - http://www.ossec.net
You are about to start the installation process of the OSSEC HIDS.
You must have a C compiler pre-installed in your system.
If you have any questions or comments, please send an e-mail
to dcid@ossec.net (or daniel.cid@gmail.com).
- System: Linux ossec-client 3.13.0-24-generic
- User: root
- Host: ossec-client
-- Press ENTER to continue or Ctrl-C to abort. --
1- What kind of installation do you want (server, agent, local, hybrid or help)? agent
- Agent(client) installation chosen.
2- Setting up the installation environment.
- Choose where to install the OSSEC HIDS [/var/ossec]:
- Installation will be made at /var/ossec .
3- Configuring the OSSEC HIDS.
3.1- What's the IP Address or hostname of the OSSEC HIDS server?: 1.2.3.4
- Adding Server IP 1.2.3.4
3.2- Do you want to run the integrity check daemon? (y/n) [y]:
- Running syscheck (integrity check daemon).
3.3- Do you want to run the rootkit detection engine? (y/n) [y]:
- Running rootcheck (rootkit detection).
3.4 - Do you want to enable active response? (y/n) [y]:
3.5- Setting the configuration to analyze the following logs:
-- /var/log/auth.log
-- /var/log/syslog
-- /var/log/dpkg.log
- If you want to monitor any other file, just change
the ossec.conf and add a new localfile entry.
Any questions about the configuration can be answered
by visiting us online at http://www.ossec.net .
--- Press ENTER to continue ---
5- Installing the system
- Running the Makefile
INFO: Little endian set.
*** Making zlib (by Jean-loup Gailly and Mark Adler) ***
[...]
*** Making cJSON (by Dave Gamble) ***
[...]
*** Making Lua 5.2 (by team at PUC-Rio in Brazi) ***
[...]
*** Making os_xml ***
[...]
*** Making os_regex ***
[...]
*** Making os_net ***
[...]
*** Making os_crypto ***
[...]
*** Making shared ***
[...]
*** Making config ***
[...]
*** Making os_maild ***
[...]
*** Making os_dbd ***
[...]
*** Making os_csyslogd ***
[...]
*** Making agentlessd ***
[...]
*** Making os_execd ***
[...]
*** Making analysisd ***
[...]
*** Making logcollector ***
[...]
*** Making remoted ***
[...]
*** Making client-agent ***
[...]
*** Making addagent ***
[...]
*** Making util ***
[...]
*** Making rootcheck ***
[...]
*** Making syscheckd ***
[...]
*** Making monitord ***
[...]
*** Making os_auth ***
[...]
- System is Debian (Ubuntu or derivative).
- Init script modified to start OSSEC HIDS during boot.
- Configuration finished properly.
- To start OSSEC HIDS:
/var/ossec/bin/ossec-control start
- To stop OSSEC HIDS:
/var/ossec/bin/ossec-control stop
- The configuration can be viewed or modified at /var/ossec/etc/ossec.conf
Thanks for using the OSSEC HIDS.
If you have any question, suggestion or if you find any bug,
contact us at contact@ossec.net or using our public maillist at
ossec-list@ossec.net
( http://www.ossec.net/main/support/ ).
More information can be found at http://www.ossec.net
--- Press ENTER to finish (maybe more information below). ---
Client OSSEC config
Adding a client to OSSEC is quite simple. First you add the client to the server, which gives you a key. Then you add this key to the client, edit the config file on the client and that's it.
First we need to generate a key on the OSSEC server for this client. We do this
by running /var/ossec/bin/manage_agents, option A, then entering the hostname,
IP and ID for the client we want to add. Do this on the OSSEC server:
root@ossec:~# /var/ossec/bin/manage_agents
****************************************
* OSSEC HIDS v2.8 Agent manager. *
* The following options are available: *
****************************************
(A)dd an agent (A).
(E)xtract key for an agent (E).
(L)ist already added agents (L).
(R)emove an agent (R).
(Q)uit.
Choose your action: A,E,L,R or Q: A
- Adding a new agent (use '\q' to return to the main menu).
Please provide the following:
* A name for the new agent: ossec-client1
* The IP Address of the new agent: 2.3.4.5
* An ID for the new agent[001]:
Agent information:
ID:001
Name:ossec-client1
IP Address:2.3.4.5
Confirm adding it?(y/n): y
Agent added.
Get the key for the OSSEC client:
root@ossec:~# /var/ossec/bin/manage_agents
****************************************
* OSSEC HIDS v2.8 Agent manager. *
* The following options are available: *
****************************************
(A)dd an agent (A).
(E)xtract key for an agent (E).
(L)ist already added agents (L).
(R)emove an agent (R).
(Q)uit.
Choose your action: A,E,L,R or Q: E
Available agents:
ID: 001, Name: ossec-client1, IP: 2.3.4.5
Provide the ID of the agent to extract the key (or '\q' to quit): 001
Agent key information for '001' is:
SD[...]AAUjd=
** Press ENTER to return to the main menu.
Then switch to the OSSEC client and execute the manage_agents:
root@ossec:~# /var/ossec/bin/manage_agents
****************************************
* OSSEC HIDS v2.8 Agent manager. *
* The following options are available: *
****************************************
(I)mport key from the server (I).
(Q)uit.
Choose your action: I or Q: i
* Provide the Key generated by the server.
* The best approach is to cut and paste it.
*** OBS: Do not include spaces or new lines.
Paste it here (or '\q' to quit): SD[...]AAUjd=
Agent information:
ID:001
Name:ossec-client1
IP Address:2.3.4.5
Confirm adding it?(y/n): y
Added.
** Press ENTER to return to the main menu.
Check if this in the /var/ossec/etc/ossec.conf file:
<client>
<server-hostname>1.2.3.4</server-hostname>
</client>
Where 1.2.3.4 is your OSSEC server URL or IP.
Now restart OSSEC on both the OSSEC server and the newly added client:
/var/ossec/bin/ossec-control restart
Repeat these steps for any client that needs to be added.
Bonus Tips
Here are a few bonus tips/config examples for OSSEC
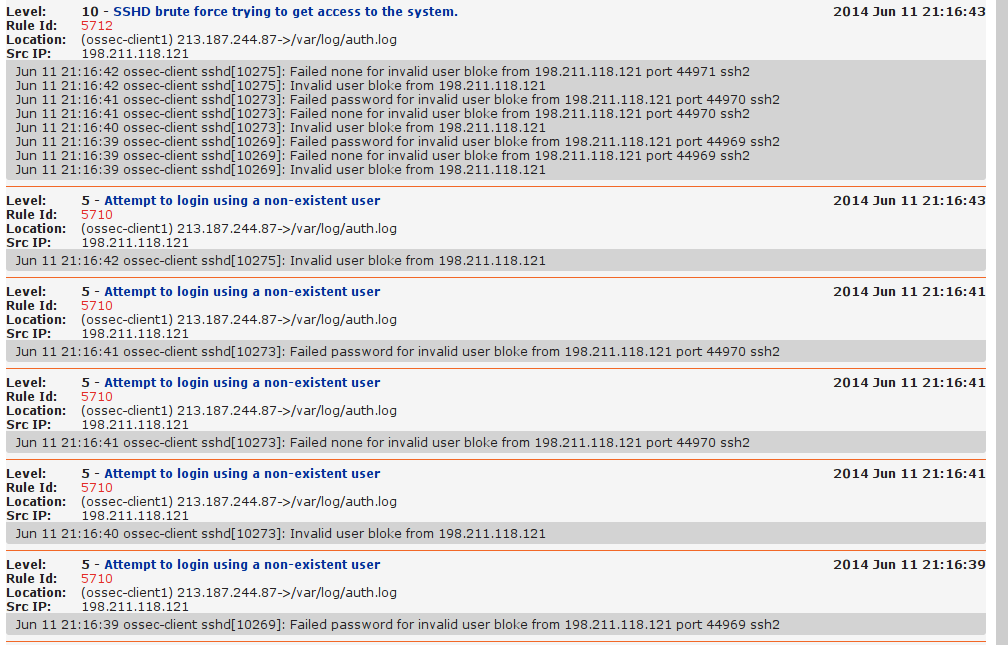
Active Response
If you've enabled Active Response you are protected from brute force attacks for ssh and some other pieces of software. Try it, login as a nonexistent user and check the web ui and logging:
tail -f /var/ossec/logs/active-responses.log
Wed Jun 11 21:16:43 CEST 2014 /var/ossec/active-response/bin/host-deny.sh add - 198.211.118.121 1402514203.20760 5712
Wed Jun 11 21:16:43 CEST 2014 /var/ossec/active-response/bin/firewall-drop.sh add - 198.211.118.121 1402514203.20760 5712
On Linux it is just a standard iptables DROP rule for that IP. You can delete the DROP rule by first finding out it's ID:
iptables -L -n --line-numbers
Chain INPUT (policy ACCEPT)
num target prot opt source destination
1 DROP all -- 198.211.118.121 0.0.0.0/0
Chain FORWARD (policy ACCEPT)
num target prot opt source destination
1 DROP all -- 198.211.118.121 0.0.0.0/0
Chain OUTPUT (policy ACCEPT)
num target prot opt source destination
Then you can delete the rule with that ID:
iptables -D INPUT 1
iptables -D FORWARD 1
Ignoring rules
To very simply ignore rules based on rule id, add them to the XML file located
in /var/ossec/rules/local_rules/xml, either on the ossec client for one
machine or the ossec server to ignore on all machines:
<!-- Specify here a list of rules to ignore. -->
<!-- 3334 postfix start -->
<!-- 3333 postfix stop -->
<rule id="100030" level="0">
<if_sid>3333, 3334</if_sid>
<description>List of rules to be ignored.</description>
</rule>
Monitoring additional log files
The OSSEC agent by default only monitors a few log files. To add more, edit the
/var/ossec/etc/ossec.conf file and add a line like this:
<localfile>
<location>/var/log/*</location>
<log_format>syslog</log_format>
</localfile>
This will add all files under /var/log. This might be a lot, you can also just
add multiple <localfile> blocks with filenames.
Firewall
You need to allow UDP port 1514 between OSSEC server and clients. Otherwise you get errors like this:
2013/09/06 19:53:00 ossec-agentd: INFO: Using IPv4 for: 10.0.51.31 .
2013/09/06 19:53:21 ossec-agentd(4101): WARN: Waiting for server reply (not started). Tried: 'ossec.raymii.nl/10.0.51.31'.