Raymii.org

Quis custodiet ipsos custodes?Home | About | All pages | Cluster Status | RSS Feed
Get number of incoming connections on specific port with ss
Published: 25-08-2020 | Last update: 07-11-2020 | Author: Remy van Elst | Text only version of this article
❗ This post is over four years old. It may no longer be up to date. Opinions may have changed.
Recently I had to write a few monitoring plugins, one of which was a count of
incoming established connections to a specific network port. In the past I
would have used netstat and a combination of grep and wc to filter out only
specific ports and established connections, but nowdays netstat is replaced by
ss on ubuntu. ss has options to filter directly on all sorts of stuff, like
state, ports, protocol, making the command I use more readable and use less
pipes.
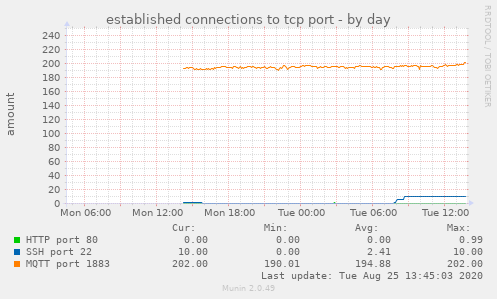
Here's an example of the graph my code makes:
[If you like this snippet, consider sponsoring me by trying out a Digital Ocean VPS. With this link you'll get $100 credit for 60 days). (referral link)][99]
The below snippet is from one of my webservers. You can check the manpage for more information, they have another quite elaborate example:
ss -o state fin-wait-1 '( sport = :http or sport = :https )' dst 193.233.7/24
List all the tcp sockets in state FIN-WAIT-1 for our apache to network 193.233.7/24
and look at their timers.
connection filtering with ss
This is the command, it even works for non-root users, which was nice since my monitoring plugins do not run as root.
ss --all --numeric --no-header state established '( sport = :443 )'
Output:
tcp 0 0 128.199.39.10:443 178.200.216.97:55467
tcp 0 0 128.199.39.10:443 137.8.9.12:39760
tcp 0 0 128.199.39.10:443 213.64.253.119:57065
To count, just add wc -l:
ss --all --numeric --no-header state established '( sport = :443 )'| wc -l
Output:
4
Change the port or add more filters, '( sport = :443 or sport = :80 )' (mind
the trailing space after the port number), you should be able to figure it out.
netstat version
On a system that still has netstat, I use the following command:
netstat -anp | grep :443 | grep ESTABLISHED | wc -l
Long running connections
Update: 2020-11-08
If you want to measure long running connections, a somewhat working example is the following:
comm -1 -2 <(ss --all --numeric --no-header state established '( sport = :443 )' | awk '{print $5}' | awk -F: 'NF{--NF};1' | sort -u) <(sleep 5; ss --all --numeric --no-header state established '( sport = :443 )' | awk '{print $5}' | awk -F: 'NF{--NF};1' | sort -u) | wc -l
The comm command is a reverse diff (show all things in common), -1 and
-2. The command executed is the same, only the last command has a sleep 5
in front of it:
ss --all --numeric --no-header state established '( sport = :443 )' | awk '{print $5}' | awk -F: 'NF{--NF};1' | sort -u
It prints all established connections to port 443, strips out the part after the last colon (the two awk commands) so that it works with IPv6 as well and then sort the list, removing duplicates. NATted connections will be counted once.
This way, you get all IP addresses that have an established connection for at least 5 seconds in your graph.
I'm using this as a brute force way to measure video live stream viewers.
Regular web requests almost never get into established, but these long
running connections do.